Advanced threat intelligence. Experts defending your business. 24/7 security to respond to cyber threats and incidents.
Need Comprehensive Coverage?
Get digital risk management and cyber insurance coverage for cyber incidents against substandard security controls








Around-the-Sun Coverage
Our Experts, Your Security
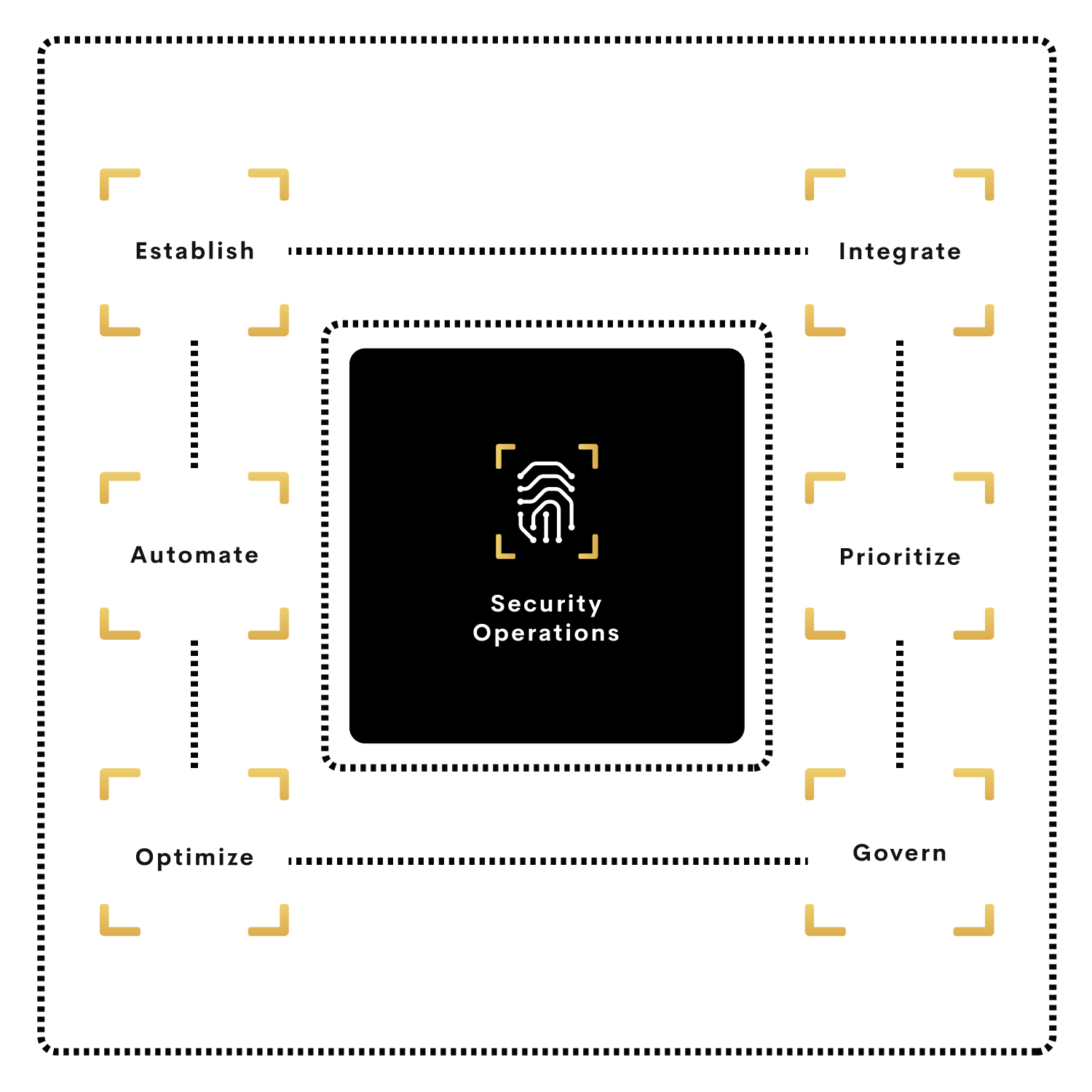
Digital Team Six (DT6) security operations center (SOC) is a 24×7 distributed facility dedicated to and organized to prevent, detect, assess, and respond to cybersecurity threats and incidents, and to fulfill and assess regulatory compliance.
- High Efficacy detections and correlations enabled by constant endpoint cybersecurity detection and response capabilities enabled with advanced AI detection and analysis relevant to customer topology, industry threats, and user behavior.
- Faster root cause and applicable actions are achieved by coupling endpoint detections along with additional telemetry from the customer’s environment and automation.
- Simplified timely actions on cybersecurity incidents for end-users and management are driven by cross control response enhanced with all integration control points across on-premise and cloud environments.
- Deeper investigation and cross-tool threat hunting from a unified, interactive view of cybersecurity posture relevant to industry threat intelligence and known customer technology security posture.
- Cost-effective cybersecurity posture improvement by employing modular multi-vendor security technology integration and removing the requirement to replace the existing security technology stack.
Powerful Threat Management and Vigilance
Eliminate your cybersecurity risks and augment your security operations
Endpoint-centric approach
Endpoint detection and response capabilities enabled with advanced AI detection and analysis to yield high-efficacy detections and correlations relevant to customer topology, industry threats, and user behavior.
Automated root cause analysis
Coupling endpoint detections along with additional telemetry from the customer’s environment and automation, DT6 SOC gets to the root cause faster and directs applicable action to the customer.
Cross control response
Cybersecurity incident response enhanced with a relevant response to the customer environment encompass all integration control points allowing simplified actions for end-users and management.
Cross tool threat hunting
Configure and integrate multiple security technology vendor solutions into reducing the requirement to replace existing security technology stack and enabling cost-effective cybersecurity posture improvement.
Threat Intelligence
Identify Risk faster in your security solutions resulting in less time to respond to threats where seconds matter. A threat intelligence solution that automates data collection and processing helps reduce this burden and allows analysts who do not have as much expertise to work more effectively.
- Automatically identifying and dismissing false positives
- Enriching alerts with real-time contexts, like custom risk scores
- Comparing information from internal and external sources


Security Operations Platform
We differentiate by providing tailored cybersecurity awareness training to industry, and regulatory standards and to meet Cybersecurity insurance requirements.
- Focus on malicious threats more quickly and accurately
- Manage vulnerabilities that are relevant to that enterprise
- Defenses, triage, and controls placed for cyber-attacks


Endpoint detection and response
Improve your business’s overall security and cyber health against vulnerabilities. Identify actual risks by combining Security Operations, Threat Intelligence, and Risk Analysis to provide additional context about the TTPs of threat actors.
- Find attack vectors combined through file trajectory and process hierarchy
- Process-based events help analysts better understand process malicious behavior
- Drill down into endpoints for insight when investigating attack vectors


Reporting and Cyber Risk Analysis
Organizations need to focus not just on providing information but on making it actionable and fostering a culture of security. Only then can long-lasting changes be made that can reduce risk by having employees make informed choices.
- Measures quantified information and security results
- Automatically receive overview reports on cyber health
- Push updates to patch vulnerabilities to improve I.T. hygiene


LEARN MORE
Get Assigned Your Dedicated Analyst and Threat Hunter From Our SOC Services
Request a demo
During your demo, we'll cover the following:
- Explore your existing security operations
- Demo Team Six modular technologies in action
- Introduce the threat monitoring systems
- Share compromised employee credentials statistics
- Address your questions about our solution