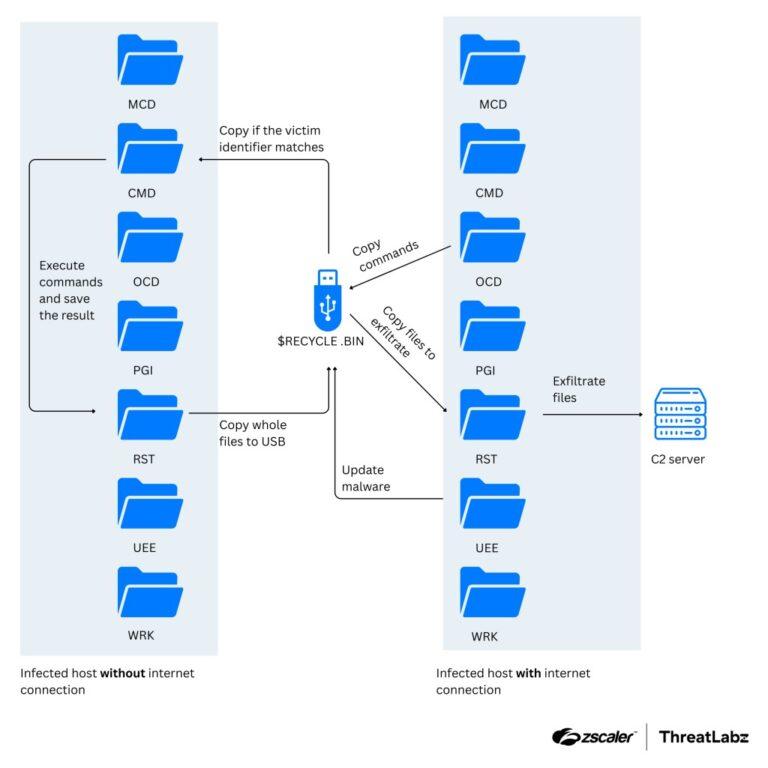
In December 2025, Zscaler ThreatLabz discovered North Korea state sponsored group APT37 employing malicious campaign called Ruby Jumper that’s capable of data exfiltration from air-gapped networks.
Detailed threat scenario from Zscaler research: APT37 Adds New Tools For Air-Gapped Networks | ThreatLabz
Use of malicious external hard drive / USB is nothing new, but this is a sophisticated threat scenario capable of creating a malicious bridge for air gapped network segments that’s typically used in critical infrastructure and industrial control systems implementations.
APT37 THUMBSBD attack flow for air-gapped systems